The Aerospace Corporation has released SPARTA v3.2, further strengthening its role as a practical, threat‑informed framework for securing modern space missions against sophisticated cyberattacks.
This new version refines the way engineers connect adversary behaviors, defensive controls, and detection artifacts across the full space architecture, from ground segment to on‑orbit payloads.
Why SPARTA Still Matters for Space Programs
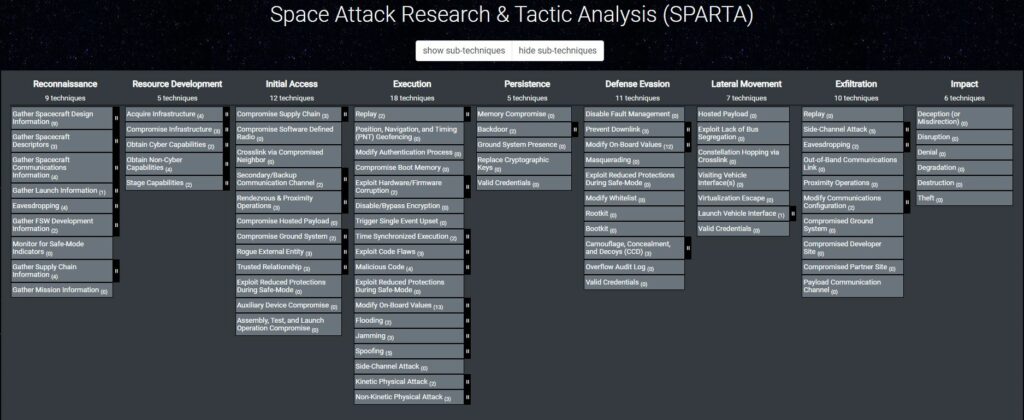
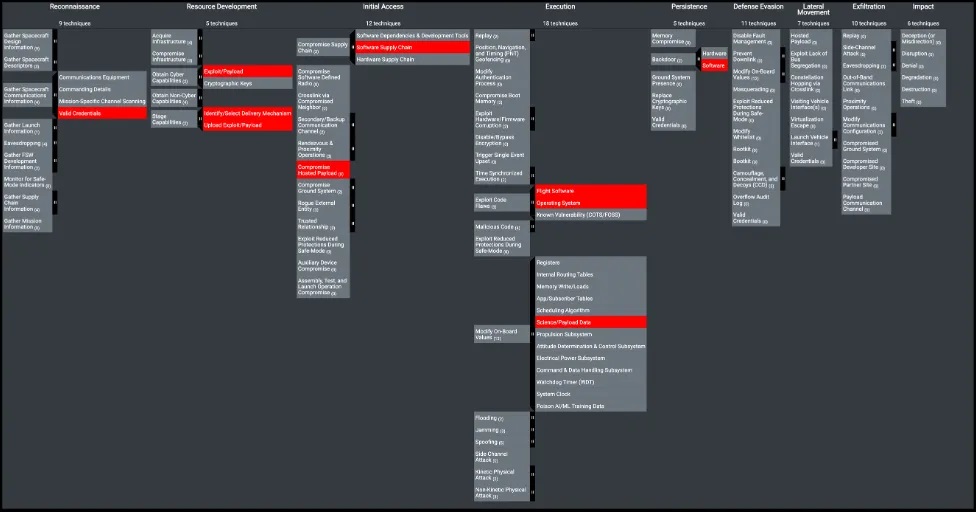
SPARTA (Space Attack Research and Tactic Analysis) is an ATT&CK‑like knowledge base dedicated to cyber threats targeting spacecraft and space systems.
It provides a structured matrix of techniques, countermeasures, and indicators of behavior (IOBs) that helps mission teams move from generic security requirements to concrete, space‑specific threat models and mitigations.
In recent years, SPARTA has become a reference for space‑cybersecurity practitioners because it:
- Describes how real adversaries operate across the space mission lifecycle, not just at the IT perimeter.
- Bridges policy and engineering by mapping techniques to NIST controls, CNSS guidance, and other standards relevant to space programs.
- Enables threat‑informed engineering, linking attack techniques directly to subsystem protections and detection strategies.
SPARTA v3.2 builds on this foundation with targeted improvements that make the framework more actionable for system engineers, mission architects, and security operations teams.
Key Enhancements in SPARTA v3.2
SPARTA v3.2 focuses on improving clarity, consistency, and operational usability across the framework’s content and tooling.
While previous releases introduced major new capabilities (such as dedicated NIST space segment guidance and new IOBs), this version consolidates that progress into a more robust and user‑friendly baseline.
Among the main updates highlighted in the official announcement:
- Refined technique and countermeasure content
SPARTA v3.2 includes editorial and structural updates to several existing techniques and countermeasures to improve naming consistency, descriptions, and relationships across the matrix.
This helps practitioners more quickly identify relevant entries for their specific mission scenarios and reduces ambiguity when performing threat modeling or control mapping. - Improved cross‑mapping hygiene
The release tightens the way SPARTA objects reference external taxonomies such as NIST SP 800‑53, CNSSI overlays, and related guidance, ensuring that mappings remain aligned with the latest space‑segment interpretations.
For security architects, this means smoother traceability from high‑level requirements down to concrete mitigations tied to SPARTA techniques. - Bug fixes and data quality improvements
As with previous iterations, SPARTA v3.2 incorporates corrections to metadata, relationships, and UI behavior discovered by users and the Aerospace team.
These changes are less visible than new techniques, but they directly improve the reliability of SPARTA‑based analyses and automation pipelines.
Even if v3.2 does not radically expand the matrix, it significantly sharpens the consistency and operational value of the existing content.
Practical Impact for Space‑Cyber Engineers
For engineers already using SPARTA for space threat modeling, v3.2 is an opportunity to refresh models, scripts, and training material against a more stable baseline.
Teams that map SPARTA techniques to their own internal control catalogs or test cases should consider re‑syncing to the updated data set to benefit from the clarified descriptions and mappings.
Concretely, SPARTA v3.2 helps:
- Make risk discussions with program management more concrete, by using clearer technique language and more precise references to external standards.
- Align design reviews and security controls with the latest thinking on space segment cybersecurity, without losing the ATT&CK‑style structure engineers are familiar with.
- Support downstream tooling, such as SPARTA‑powered detection or assessment platforms, that rely on consistent identifiers and relationships.
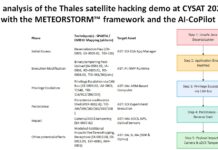
An example use case is a mission team updating its threat model for a new satellite bus: by re‑baselining on SPARTA v3.2, they can ensure that techniques, countermeasures, and mapped controls reflect the current Aerospace guidance and community feedback.
Looking Ahead
The SPARTA roadmap over the last few years (from v3.0 to v3.2) shows a clear trend: iterative, practical improvements that keep the framework aligned with evolving space‑cyber threats and policy updates.
Instead of one‑off releases, SPARTA is evolving as a living, curated knowledge base that the space community can depend on for threat‑informed engineering.
As space missions grow more complex and interconnected, having a stable yet continuously refined framework like SPARTA v3.2 is essential for bridging the gap between high‑level standards and real‑world adversary behavior.
If you are working on space mission cybersecurity and have not revisited SPARTA recently, this new version is a good moment to do so and to integrate it more deeply into your architectures, reviews, and training workflows.
To go further
Thank’s to Brandon Bailey, Dan Painter, Brad Roeher and Randi Tinney from The Aerospace Corporation for this major SPARTA update.