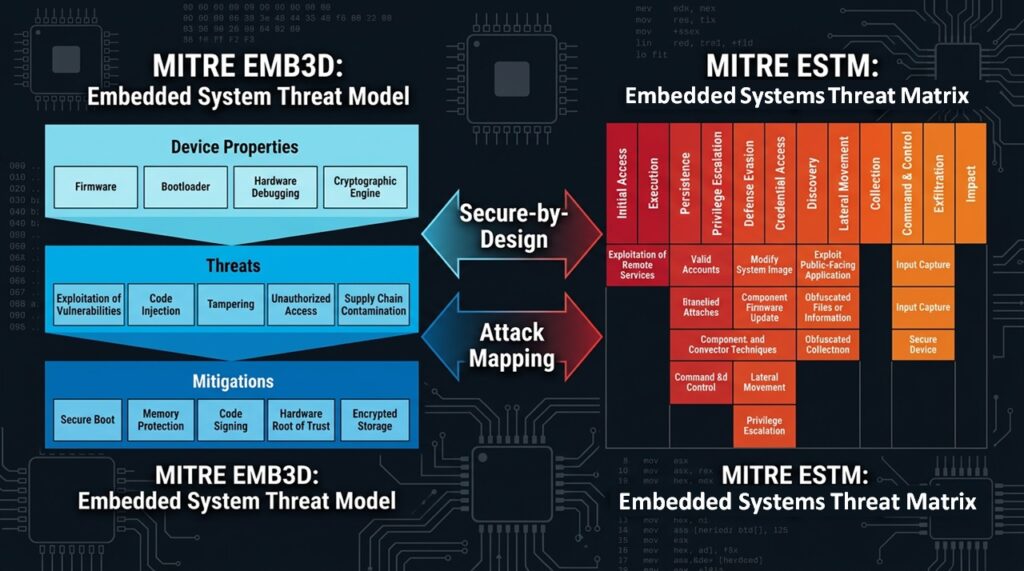
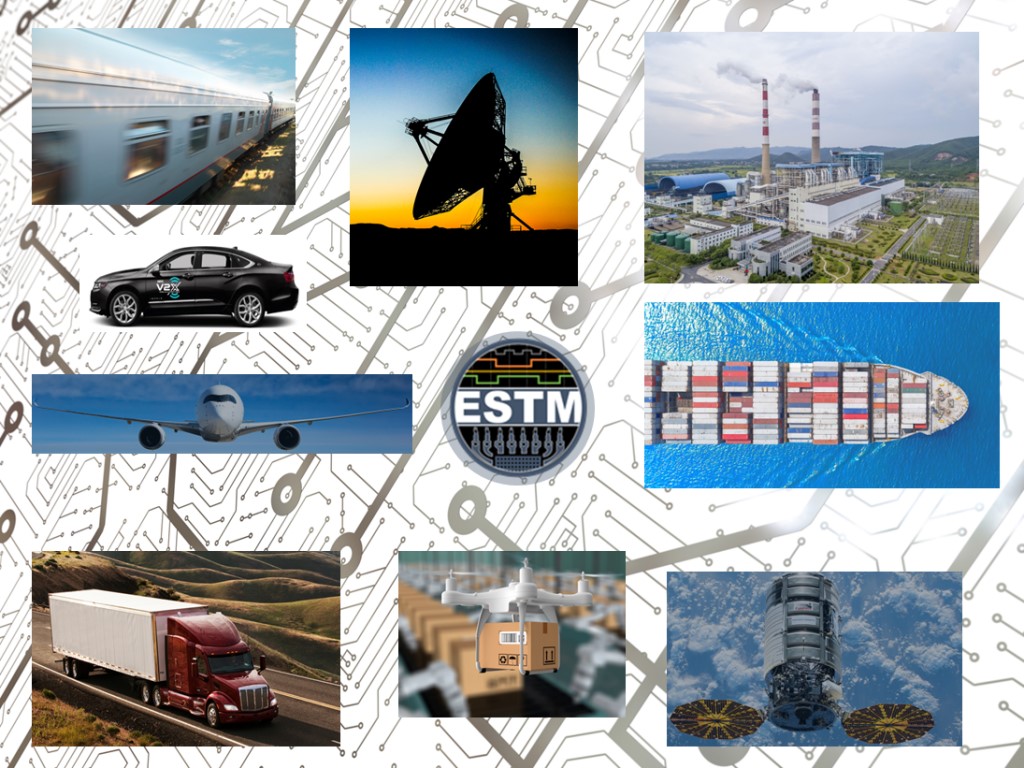
Recently, MITRE released ESTM (Embedded Systems Threat Matrix), a new cybersecurity framework designed to protect embedded systems. Built on the proven ATT&CK® methodology, ESTM organizes tactics and techniques (TTPs) tailored to embedded environments.
In parallel, MITRE launched EMB3D in 2024, a threat model focused on secure-by-design embedded devices, while ESTM takes an offensive approach as an attack matrix.
This article explores how ESTM and EMB3D can work together for comprehensive embedded system defense.
ESTM and EMB3D
ESTM and EMB3D are designed to be complementary: you can use EMB3D to drive secure‑by‑design requirements and mitigations at device level, and ESTM to map real attacker behaviors and operations against those devices throughout their lifecycle.
Mental model: what each brings
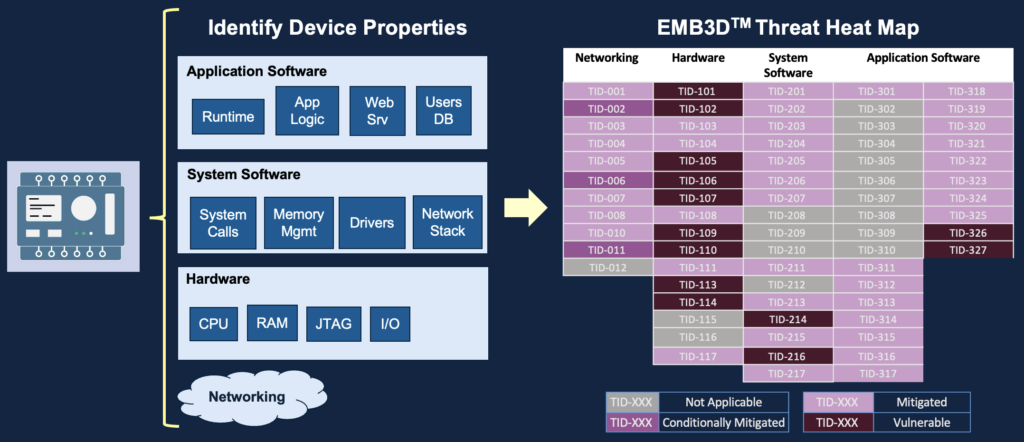
- EMB3D is a curated threat model for embedded devices that maps device properties to known threats and prescribes tiered mitigations (Foundational/Intermediate/Leading). We explore more in depth MITRE EMB3D in this article.
- ESTM is an ATT&CK‑style matrix of tactics and techniques tailored to embedded systems, focused on how adversaries actually operate (kill‑chain perspective). We explore more in depth MITRE ESTM in this article.
- MITRE explicitly states ESTM “works with” EMB3D to provide a complete resource for secure system design and defense.
Typical workflow: EMB3D → ESTM → EMB3D
1. Architecture & design (EMB3D first)
- Use EMB3D Properties to model your device (boot architecture, debug interfaces, comms stacks, safety features, etc.).
- From those Properties, enumerate relevant Threats and associated Mitigations, and derive security requirements (e.g. “protect firmware update mechanism”, “harden debug ports”).
2. Adversary behavior mapping (ESTM)
- For each EMB3D Threat, identify which ESTM tactics/techniques an attacker would likely use (e.g. Initial Access via supply‑chain, Firmware Persistence via malicious bootloader, Lateral Movement over fieldbus).
- Use this to define detection use‑cases, test scenarios, and red‑team playbooks that are realistic for embedded environments (not generic IT ATT&CK).
3. Refine mitigations and coverage (back to EMB3D)
- Take the ESTM techniques you care about most (based on threat intel, safety impact, mission impact) and check whether EMB3D’s mitigations and tiers give you enough depth for each mapped Threat.
- Where there is an ESTM technique with weak or missing mitigations in your design, prioritize closing those gaps using EMB3D’s mitigation guidance, aligned where relevant with ISA/IEC 62443‑4‑2.
A simple example:
- EMB3D says: your MCU exposes unauthenticated debug/UART (Property → Threat “unauthorized debug access”) and recommends mitigations like physical protection, debug lock, and authenticated debug unlock.
- ESTM lets you express how an attacker would use that in a campaign: Reconnaissance (locating interface), Initial Access (physical or proximity), Credential Access (dump secrets via debug), Persistence (modifying firmware), and Impact (tampering with control logic).
- You can now:
- Turn those ESTM techniques into test cases for lab exploitation and purple‑team exercises.
- Use EMB3D’s mitigation tiers to decide what level (Foundational vs Leading) you need based on your risk appetite and safety context.
Role split: secure‑by‑design vs operations
- Product / system engineers
- Primary lens: EMB3D to capture device properties, threats, and mitigation roadmaps across product generations.
- ESTM used to ensure requirements consider concrete adversary workflows and to validate that design controls actually break likely attack chains.
- Blue / red / purple teams & OT SOC
- Primary lens: ESTM to model attack paths, prioritize monitoring at firmware/boot/fieldbus levels, and build detection content.
- EMB3D used as the “defensive catalogue” to validate that for each high‑value tactic/technique they are trying to detect, the underlying device has the right mitigations or compensating controls.
Practical integration ideas
- Bidirectional mapping: maintain an internal mapping table: EMB3D Threat IDs ↔ ESTM tactics/techniques, plus links to ATT&CK where relevant, so you can pivot between design, testing, and SOC views. (MITRE notes EMB3D already aligns with ATT&CK/CWE/CVE, which helps here.)
- Tooling and STIX: EMB3D 2.0 provides a STIX 2.1 JSON format, enabling ingestion into threat/vuln tooling; you can extend that repo with fields for associated ESTM techniques to keep everything in one knowledge base.
- Standards alignment: use EMB3D’s 62443‑4‑2 alignment to show compliance of mitigations, while ESTM scenarios feed into security test plans and evidence for those same controls.
Exploring recent studies
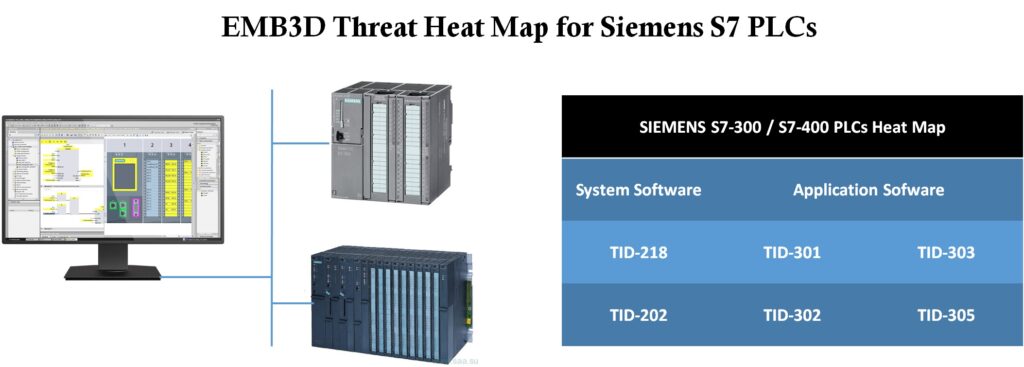
In this article, I show how I used the MITRE EMB3D™ Threat Model to identify vulnerabilities in SIEMENS PLCs that were exploited by the Stuxnet worm to sabotage the Iran’s nuclear centrifuges.
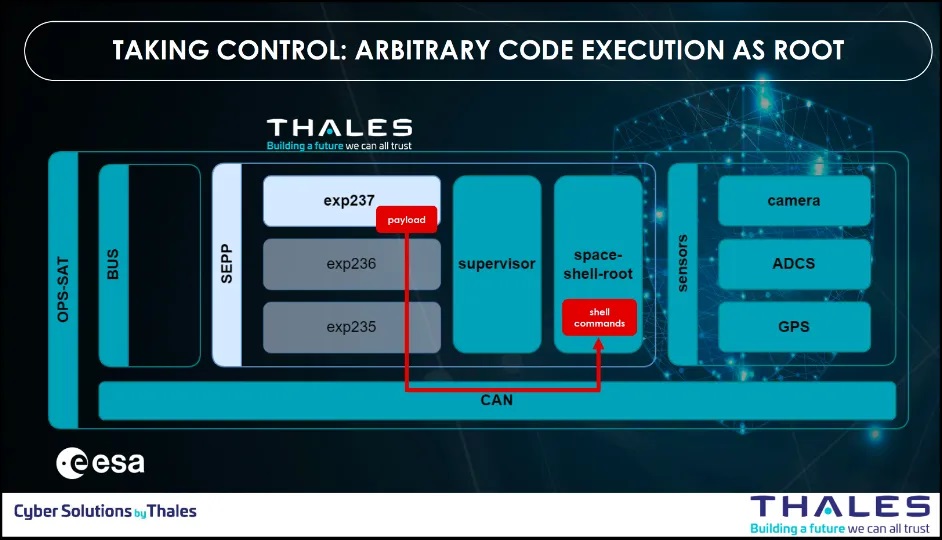
In this article, I show how I used the MITRE EMB3D™ Threat Model to break down the experiment of Thales satellite hacking demo at CYSAT 2023, identify key lessons learned, and record possible countermeasures.