23 Tips to Pass CCSK (Certificate of Cloud Security Knowledge) from CSA at the...
At the beginning of April 2020, I successfully passed the CCSK certification (Certificate of Cloud Security Knowledge). Now, I give you some tips and...
Enhancing Threat Understanding: Modeling the Viasat Cyber Attack with MITRE CTID’s Attack Flow Builder
Introduction
In the complex landscape of modern cybersecurity, understanding the intricate mechanisms of sophisticated cyber attacks has become paramount.
On February 24, 2022, Viasat, a global...
My experience and tips after successfully passed the CISM (Certified Information Security Manager) from...
🌟 I'm thrilled to share that I've earned the CISM (Certified Information Security Manager) from ISACA. You can view my achievement on Credly.
🌍 This...
La chine réalise la première communication sécurisée par cryptographie quantique basée sur l’intrication depuis...
Selon une étude publiée le 15 juin dans la revue Nature, des scientifiques chinois ont réalisé la première distribution de clés quantiques au monde...
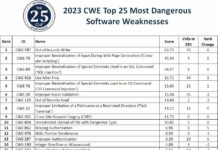
Top 25 most dangerous software weaknesses than can affect satellites in 2023
Issues of vulnerabilities of space systems to cyber attacks has long been ignored for reasons common to industrial systems or SCADA (Supervisory Control And...
Thales confirms its key role to provide cybersecurity for Galileo second generation to meet...
Thales has been notified by the European Space Agency (ESA), on behalf of the European Union Agency for the Space Programme (EUSPA) and the...
DroneSec, a private intelligence agency for drone threats, that provides UAS Threat Intelligence and...
DroneSec is a private intelligence agency for drone threats. DroneSec provides drone threat intelligence solutions to protect people and drones from malicious drones and...
« Aerospace Cybersecurity: Satellite Hacking » course review
I just successfully completed the comprehensive course on « Aerospace Cybersecurity: Satellite Hacking » and passed successfully the final exam with a result of...
Exploring the power of the METEORSTORM™ framework — a framework built for full-spectrum modeling...
I'm very proud to have successfully taken up a new challenge exam in beta version about METEORSTORM™ framework which allowed me to obtain the...
Solarium CSC 2.0 has endorsed designation of space systems as a critical infrastructure sector
The Cyberspace Solarium Commission (CSC) was established in the John S. McCain National Defense Authorization Act for Fiscal Year 2019 to "develop a consensus...