Introduction
In this paper, I choose to investigate the Viasat cyber attack that occurred on 24 February, 2022. First, I will summarize the chronology of events (Chapter 1). Then, I will try to critique the organization’s response to the cyber attack (Chapter 2). After that, I will suggest additional steps that could have been taken to further mitigate the impact moving forward (Chapter 3). Finally, I will think about what the attacked organization could have done beforehand to prevent the attack (Chapter 4).
Disclaimer, details and references
To do this analysis of the Viasat cyber attack, I used 3 articles, documents or papers detailed below:
- [1] Space Cybersecurity Lessons Learned from The ViaSat Cyberattack from Nicolò Boschetti (Cornell University), Nathaniel Gordon (Johns Hopkins University) and Gregory Falco (Cornell University)
- [2] KA-SAT Network cyber attack overview by Viasat
- [3] AcidRain | A Modem Wiper Rains Down on Europe by SentineOne Team
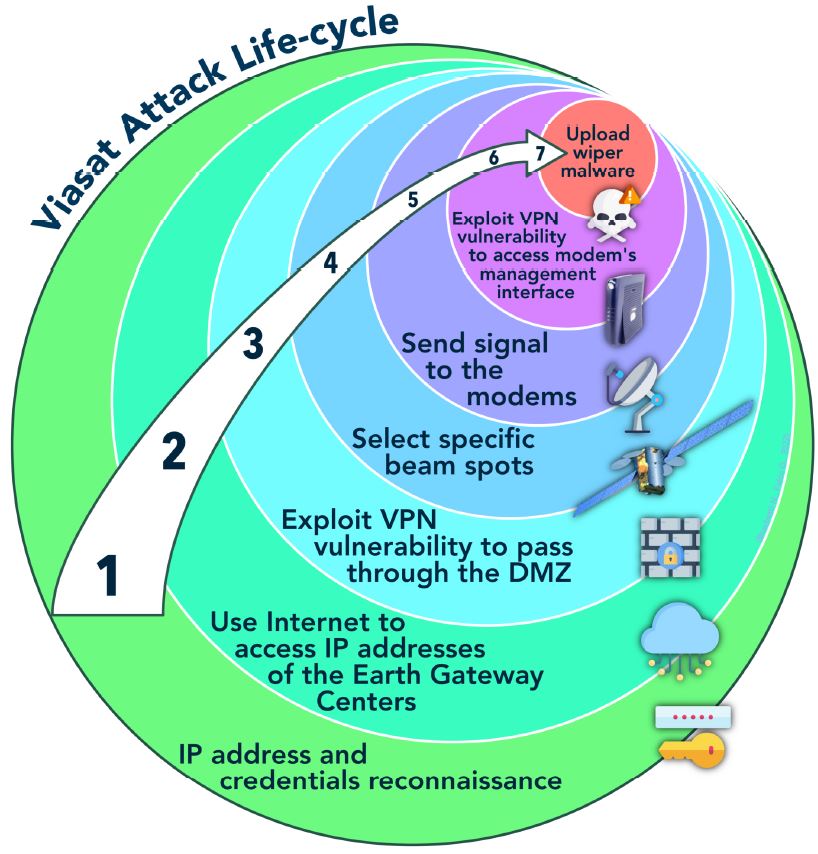
First, I used the open-source intelligence (1) of the team composed by Nicolò Boschetti (Cornell University), Nathaniel Gordon (Johns Hopkins University) and Gregory Falco (Cornell University). In their open-source intelligence, they reconstructed the lifecycle of the attack. They specified that however, without first-hand knowledge of ViaSat’s systems, they cannot be certain about their hypothesis.
Viasat’s statement (2) on Wednesday, March 30th, 2022 provides a somewhat plausible but incomplete description of the attack. In a statement disseminated to journalists (3), Viasat confirmed the use of the AcidRain wiper in the February 24th attack against their modems.
At the DefCon 31, Mark Colaluca and Nick Saunders from Viasat presented a talk named Defending KA-SAT. During this talk, they argued not to believe everything that you can read on the internet. It’s often simply inaccurate. They told that there is no evidence or proof of the claims. There is no evidence of any compromise or tampering with Viasat modem software or firmware images and no evidence of any supply-chain interference. Regarding, the possibility that wiper-malware was deployed and erased the hard drives of the modems, they answered that modems don’t have hard drives.
1. Summary of chronology of events
The Ukrainian conflict shown the potential and temptation of targeting space assets during an armed conflict between two states. Telecommunications satellites are vital to both national security and the economy. But unfortunately, they are also increasingly vulnerable to cyber-attacks and increasingly targeted by malicious actors.
Regarding the Ukrainian conflict, one example is the cyber-attack on the Viasat satellite company.
The Viasat attack was a cyberattack on American communications company Viasat affecting their KA-SAT network, on 24 February, 2022. Thousands of Viasat modems got hacked by a deliberate cyber event. Thousands of customers in Europe, especially in Ukraine, have been without internet for a month since.
Viasat is an American communications company based in Carlsbad, California, with additional operations across the United States and worldwide. Viasat is a provider of high-speed satellite broadband services and secure networking systems covering military and commercial markets.
This attack began approximately one hour before Russia launched its major invasion of Ukraine. UK and US intelligence assesses that Russia was almost certainly responsible for the attack.
According to Viasat, the attacker used a poorly configured virtual private network appliance to gain access via internet to the trusted management part of the KA-SAT network.
The vulnerability used by the attackers is CVE-2018-13379, corresponding to a vulnerability in the Fortinet firewall discovered in 2019.
Once on the trusted management segment of the KA-SAT network, the attackers issued commands to select specific beam spots and then signal to the modems.
They overwrote part of the flash memory in modems, making them unable to access the network, but not permanently damaged. The satellite itself and its ground infrastructure were not directly affected.
With their open-source intelligence, the team [1] (Nicolò Boschetti, Nathaniel Gordon and Gregory Falco) schematized the entire attack lifecycle in the diagram below.
2. Criticism of the organization’s response to the cyber attack
ViaSat seems to be a company with dual-use satellites – satellites that can serve both civil and military. Presumably, Viasat was not prepared to be a military target in. I think that dual-use commercial space companies must be aware and prepared to be a military target in.
Viasat also appears to be a geographically dispersed organization. The ground segment of Viasat is called KA-SAT Network. Launched and owned by Eutelsat, the KA-SAT network was acquired by ViaSat in 2020. During the acquisition transition period, the management of the ground segment was still in the hands of the Eutelsat subsidiary Skylogic. Each subsidiary is responsible for different elements of the KA-SAT infrastructure.
This organizational complexity makes challenging to have homogenous security controls and the geographic dispersion of the organizations and their integration through corporate acquisition did not help with the managerial coordination of the attack response. When responding to the attack, there was an apparent lack of coordination of ViaSat, Eutelsat, and Skylogic.
3. Additional suggestions that could have been taken to further mitigate the impact moving forward
As additional steps that I can suggest is the need for an agile and software-enabled strategy to quickly respond to attacks. Indeed, the AcidRain wiper malware resulted in the development of a lot of inoperable modems. Shipping tens of thousands of modems is undoubtedly time-intensive and costly.
Given the critical nature of the satellite communication system, it is unacceptable for such a delay. Viasat need to deploy a better agile response to attack like the possibility to deploy a software update that was developed to restore access for users.
4. What the attacked organization could have done beforehand to prevent the attack
This attack is a concrete example of malicious operations carried out by a group of adversaries during a space-cyber war.
To combat cyber-attacks on space systems, states should adopt national policies to defend against threats to space-based assets and applications. This won’t prevent space-cyber hostilities, but it could provide protections against space-cyber threats.
Verification and Validation before launch are also very important. Space systems, once launched and deployed, are subject to limitations around structural modifications. For example, Terminals, Modems or End User Equipment are not easily replaced or modified.
Viasat should also do penetration testing in order to test robustness before deploying their equipment. They also need to ensure there equipment are hardening as the good security level.
Viasat need to do threat modelling for Space Systems. Threat modelling plays a crucial role in risk mitigation. Threat modelling helps to identify the security requirements of a system or process and is far more cost-effective than reacting to a breach or attack
Viasat need also to do security risk analysis. Risk analysis allows to identify risk and their likelihood and impact on a system. Risk analysis allows also to identify mitigation plan to reduce risks.
Viasat as satellite providers must be concerned about its supply chains and vendor ecosystems. Given the critical nature of the satellite communication system, Viasat need to monitor its supply chain. Supply chain has been identify by ENISA, the European Union Agency for Cybersecurity, as the mainly attack threat vector in 2021. Viasat should engage in supply chain security best practices such as conducting extensive vendor cybersecurity evaluations.
Finally, Viasat should establish a strong patch management program in order to maintain a regular security update.
Main References
- [1] Space Cybersecurity Lessons Learned from The ViaSat Cyberattack from Nicolò Boschetti (Cornell University), Nathaniel Gordon (Johns Hopkins University) and Gregory Falco (Cornell University)
- [2] KA-SAT Network cyber attack overview by Viasat
- [3] AcidRain | A Modem Wiper Rains Down on Europe by SentineOne Team














[…] Källa: https://www.spacesecurity.info/en/space-cyber-attack-post-mortem-a-viasat-attack-investigation/ […]