Space and Satellites Security Conferences at DEF CON 32 (and a little bit Aviation...
The videos from the Def Con 32 conference held in Las Vegas from August 8th to 11th are now online. Perfect for keeping busy...
Description of the Elements of a Satellite Command and Control System
In order to be able to analyse the various threats and identify the risks facing a space system, it is necessary to describe precisely...
CYSAT ’21, a space cybersecurity conference : Full Keynotes and Presentations
CYSAT ’21 is the first conference in Europe dedicated to satellite and space industry cyber security. It took place from 17 to 19 March...
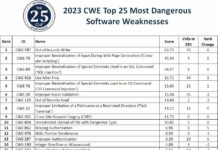
Top 25 most dangerous software weaknesses than can affect satellites in 2023
Issues of vulnerabilities of space systems to cyber attacks has long been ignored for reasons common to industrial systems or SCADA (Supervisory Control And...
ethicallyHackingspace (eHs)® h4ck32n4u75™ (Hackernauts) Community Member
I'm very proud to have been choosen as ethicallyHackingspace(eHs)® h4ck32n4u75™ (Hackernauts) Community Member. Thank's to William Ferguson for this distinction.
The "h4ck32n4u75™" badge, pronounced "hackernauts,"...
CYSAT ’22, a space cybersecurity conference in Paris (April 6-7th 2022)
CYSAT is the first European event entirely dedicated to cybersecurity for space.
After a first successful edition over 2 days in March 2021 with over...
An analysis of the Thales satellite hacking demo CYSAT 2023 by SPARTA team
Brandon Bailey & Brad Roeher from the SPARTA team analyzed, in this article, Thales Group’s CYSAT ’23 presentation material to deconstruct the experiment, extract lessons...
DEF CON 29 Aerospace Village Videos
DEF CON Aerospace Village is a researcher led, non-profit whose mission is to build a diverse community focussed on the security of everything from...
« Aerospace Cybersecurity: Satellite Hacking » course review
I just successfully completed the comprehensive course on « Aerospace Cybersecurity: Satellite Hacking » and passed successfully the final exam with a result of...
The dark side of the DNS or the war of the port 53
I am very happy and proud that my article on DNS security has been accepted and published in the last issue of Hakin9 Magazine...