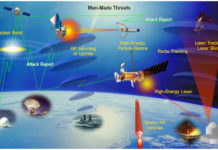
What are the threats to space systems?
In this article, we will try to identify the various threats to space systems.
This article is a synthesis of the CSIS (Center for Strategic...
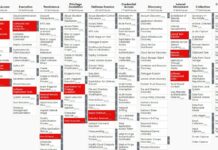
An analysis of the Viasat cyber attack with the MITRE ATT&CK® framework
Disclaimer
To do this analysis of the Viasat cyber attack, I used the open-source intelligence (1) of the team composed by Nicolò Boschetti (Cornell University),...
23 Tips to Pass CCSK (Certificate of Cloud Security Knowledge) from CSA at the...
At the beginning of April 2020, I successfully passed the CCSK certification (Certificate of Cloud Security Knowledge). Now, I give you some tips and...
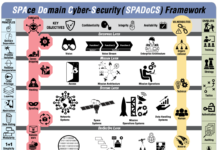
A quick comparaison of recently released Cybersecurity Frameworks for Space Sector
« The space sector is in need of frameworks and methodologies specific to our unique operating environment » said Gregory Falco (Aerospace Security & Space Technology Asst. Prof...
First CTF in space with Hack-A-Sat: the US Air Force launches a Bug Bounty...
It was the TechCrunch site that revealed the information. The U.S. Air Force will launch a bug bounty program in the form of a...
SPAce Domain Cybersecurity framework aka. SpaDoCs
The space and cyber domains have developed in parallel over the past several decades. The two domains evolved separately and have employed different architectural...
Aerospace Corporation released SPARTA v1.3, a new version of the Space Attack Research and...
Thank's to Calogero Vinciguerra (Space Policy Officer & Space Threats Response Architecture DO at the European External Action Service, EEAS) and Kimberly King (Senior...
« Aerospace Cybersecurity: Satellite Hacking » course review
I just successfully completed the comprehensive course on « Aerospace Cybersecurity: Satellite Hacking » and passed successfully the final exam with a result of...
An analysis of the Thales satellite hacking demo CYSAT 2023 by SPARTA team
Brandon Bailey & Brad Roeher from the SPARTA team analyzed, in this article, Thales Group’s CYSAT ’23 presentation material to deconstruct the experiment, extract lessons...
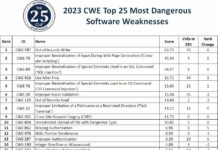
Top 25 most dangerous software weaknesses than can affect satellites in 2023
Issues of vulnerabilities of space systems to cyber attacks has long been ignored for reasons common to industrial systems or SCADA (Supervisory Control And...