Very proud to have earned the Kelley School of Business – Space Cybersecurity Professional...
I’m pleased to announce that I have obtained a new certification: Kelley School of Business Executive Education Space Cybersecurity from Indiana University - Kelley...
Back to the lastest “In-Flight Abort Test” from SpaceX before the first manned flight...
On Sunday, January 19, 2020, the last big test for SpaceX, Elon Musk's company, took place successfully. It was to simulate a failure of...
Des pirates informatiques annoncent avoir infiltré un sous-traitant de la NASA juste après le...
Les opérateurs du rançongiciel (ransomware) DoppelPaymer ont félicité la NASA ainsi que la société SpaceX d'Elon Musk pour le premier lancement d'une fusée privée...
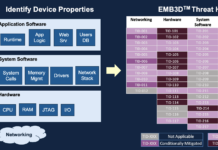
MITRE Releases EMB3D™ – A Cybersecurity Threat Model for Embedded Devices
Collaborative framework provides common understanding to mitigate cyber threats to critical infrastructure
MCLEAN, Va. & BEDFORD, Mass., May 13, 2024--(BUSINESS WIRE)--The EMB3D Threat Model is...
MITRE realeased ATT&CK v14 with improvements to Detections, ICS, Mobile
🔥 On 31 October 2023, the MITRE Corporation realeased ATT&CK v14, the new version of its framework.
This new version includes significant improvements to Detections,...
A quick comparaison of recently released Cybersecurity Frameworks for Space Sector
« The space sector is in need of frameworks and methodologies specific to our unique operating environment » said Gregory Falco (Aerospace Security & Space Technology Asst. Prof...
Aerospace cybersecurity manuals bundle : satellites, drones, airplanes, and signals intelligence systems
Angelina Tsuboi is a programmer, mechatronics developer and Engineer, a pilot, a Scientific Researcher and cybersecurity researcher. She is currently working for NASA. She...
Un chercheur alerte sur le risque de piratage des petits satellites comme ceux de...
SpaceX et d'autres sociétés se précipitent pour mettre en orbite des milliers de petits satellites bon marché, mais la pression pour maintenir les coûts...
23 Tips to Pass CCSK (Certificate of Cloud Security Knowledge) from CSA at the...
At the beginning of April 2020, I successfully passed the CCSK certification (Certificate of Cloud Security Knowledge). Now, I give you some tips and...
CyberInflight is part of the contributor list of the SPARTA framework
CyberInflight team is part of the contributor list of the SPARTA framework. The last version published on July 18, 2023, adds more than 60...