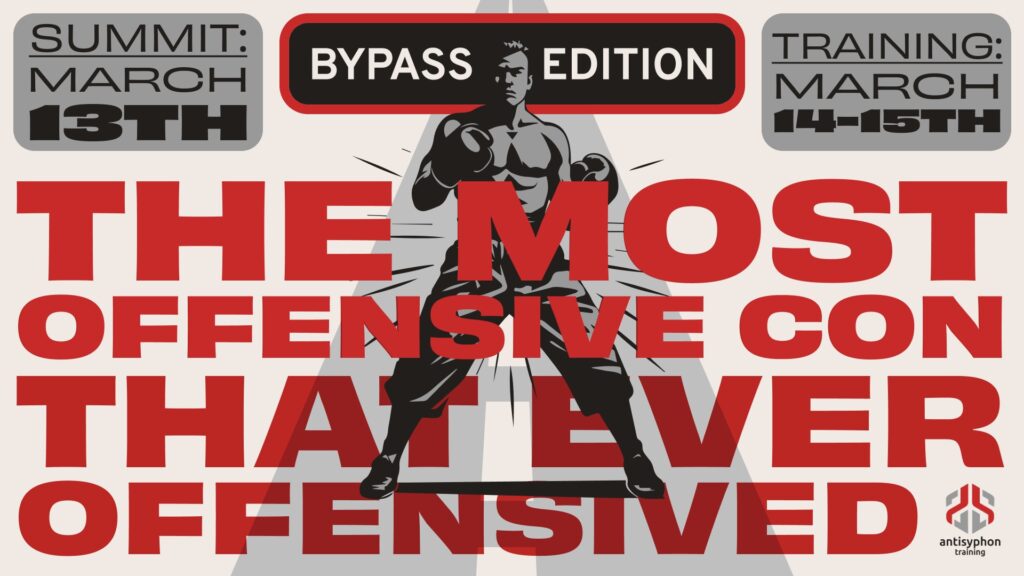
PenTest and Hakin9 are very proud to present with a special edition, created in a collaborative process between experts in the field of space cybersecurity, PenTest, and Hakin9 magazines. The topic is currently getting more and more deserved attention, and they are more than happy to bring experts’ voice to the table here.
In the “Space Cybersecurity” eBook by PenTest & Hakin9 you will read about this fascinatingarea from a variety of perspectives: from the future of optical and laser communication and its security, through cybersecurity measures in modern space exploration, simulating the test of space systems with S-WAN, end-to-end security management system using COSMOS2, Space threats and operational risks to mission, security by design for satellites, to the relevant information about ASAT, geopolitical aspects of space cybersecurity, and cybersecurity in the ground segment for space industry.
It is a great compendium of knowledge provided by the practitioners in the field. Special thanks to all the contributors, reviewers, and proofreaders involved in the creation of this issue.
Let’s launch and dive in the reading process.
TABLE OF CONTENTS
The Future of Satellite Communication: Optical Communication and Lasers. Is it Secure? from Angelina Tsuboi
Although there are a plethora of benefits that emerge from migrating to optical- based communications infrastructure, it still has some drawbacks. Firstly, optical communications rely on high precision since information is sent via a narrow beam pointed at the receiver. This significantly reduces the margin for error as even a slight deviation of the beam could result in signal disruption. Moreover, optical signals are highly vulnerable to interference found in external light emissions from various sources like the sun and other optical signals. Both of these factors make optical communications vulnerable to interception, spoofing, jamming, and physical attacks.
Cybersecurity Measures in Modern Space Exploration from Sylvester Kaczmarek
As with any computerized system, autonomous space systems are vulnerable to software-based attacks. Malicious entities could potentially introduce rogue software into these systems. Such software could subtly alter the system’s behavior, making it perform unintended actions or even sabotage its mission. For instance, a malicious software injection could alter a satellite’s data collection parameters, leading it to transmit false or corrupted data back to Earth. In the case of an autonomous rover on a distant planet, such an attack could result in it straying into hazardous terrain or failing to carry out its scientific objectives. Moreover, the specific security risks vary between different types of autonomous space systems. For instance, autonomous satellites managing Earth observation may be targeted to manipulate environmental data, while rovers exploring extraterrestrial surfaces could be commandeered to disrupt scientific discovery or misrepresent findings.
S-WAN: Simulate the Test of Space systems from Jamel Metmati
The simulation doesn’t replace the test on the real chambers once the satellite’s assembled. It provides support on the process between the preliminary design and the assembly, integration and test phase, the operational activity in space. The simulation gives an environment test to monitor and control the satellites to understand anomalies to be studied and to be corrected on short notice.
Space Threats and Operational Risks to Mission (STORM) from William Ferguson
There is a clear need for space cybersecurity workforce development that will require public, private, and international government cooperation. Significant progress is already being made with the ongoing efforts to build space cybersecurity skills through cutting-edge platforms like Moonlighter, an on-orbit cybersecurity training platform, Hack-a-Sat, and established communities like the Aerospace Village that have existed for some time. But there is still more work to be done.
End-to-End Security Management of Space Systems using COSMOS2 from Dr Jordan Plotnek
This article provides an overview of the outcomes of a multi-year research project resulting in the novel COSMOS2 (Contemporary Ontology for the Security Management of Space Systems) framework, developed through iterative feedback from space security experts across 10 countries. The framework includes a definition for space systems security and a tabular taxonomy encompassing the protection of five segments (Ground, Space, Communications, Human, and Governance) against four threat categories (Non-Malicious, Cyber, Electromagnetic, and Kinetic).
Safeguarding Earth’s Frontline: The Crucial Role of Cybersecurity in Space Operations from Olga Nasibullina
To fortify cybersecurity in space operations, there is a need for increased education. Initiatives like the European Space Agency’s collaboration with Rhea Group have led to the development of dedicated Space Operations Cyber Ranges. These ranges offer services such as preparation, testing, and training for cyberattacks, along with 24/7 managed Security Operations Centre (SOC) support. Two consortia consisting of Estonian companies are developing a concept for a space cyber training range. The first consortium includes Spaceit, CybExer, and CGI; the second includes Nortal and Talgen. Foundation CR14, established by the Estonian defense ministry, is also a member of both consortia. The new range should, among other things, allow us to simulate specific space-related environments and potential threats, validate various industry-specific components and processes, and contribute to the development of know-how related to space cyber defense.
Space Cybersecurity: a Strategic Issue in the Current Geopolitical Context from Anais Shay-Lynn Videlingum
The security of space infrastructures is a geopolitical issue, as space-based resources are increasingly used by our societies in all fields, from construction and financial markets to military capabilities. The rapid development of objects and services powered by satellites is contributing to a growing dependence on space in all fields. Being present in space has become a strategic issue over time, depending on the interest of decision-makers in the use of space. Protecting satellites in low, medium, or geostationary orbit is now a strategic asset for governments, the military, and commercial operators alike, to ensure continuity of service and guarantee a degree of resilience.
Space Oddities: What is ‘Secure-by-Design’ and Why Does it Matter for Satellites? from Mikols Tomka and Isabela Leandersson, Pasimoni and Tarides
In response to the cybersecurity agencies’ advice, some people may argue that the risks are mitigated in the context of Space IoT and edge computing because satellites are more difficult to attack. Unfortunately, this could not be further from the truth. Not only are satellites vulnerable to attack, but the infrastructure they provide is critical to many fundamental systems across the globe. Much of that critical infrastructure is, as of today, relatively unprotected!
To know more
- Read whole article HERE!
- Check a preview here