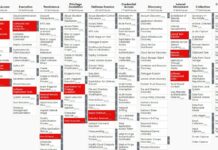
MITRE realeased ATT&CK v14 with improvements to Detections, ICS, Mobile
🔥 On 31 October 2023, the MITRE Corporation realeased ATT&CK v14, the new version of its framework.
This new version includes significant improvements to Detections,...
Very proud to have earned the Space Domain Cybersecurity digital badge from Teaching Science...
🚀 I’m proud to took part of the 3-day Space Domain Cybersecurity course provided by Teaching Science & Technology, Inc. (TSTI) in partnership with...
Live Webinar on Aerospace Cybersecurity: Satellite Hacking
Find below the first ever webinar by PenTest Mag! Hosted by Timothy Hoffman, the talk will evolve around the topic of the online course...
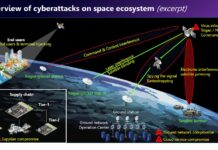
An analysis of the Viasat cyber attack with the MITRE ATT&CK® framework
Disclaimer
To do this analysis of the Viasat cyber attack, I used the open-source intelligence (1) of the team composed by Nicolò Boschetti (Cornell University),...
New upcoming course : “Aerospace Cybersecurity: Satellite Hacking” made by Angelina Tsuboi in collaboration...
We are very excited to announce a new upcoming course, "Aerospace Cybersecurity: Satellite Hacking" led by Angelina Tsuboi in collaboration with PenTestMag.
This comprehensive course...
Indiana University – Kelley School of Business launches a new academic program dedicated to...
Russia’s cyberattack on ViaSat on the eve of its invasion of Ukraine put the cyber fragility of space systems high on the agenda and...
CyberInflight is part of the contributor list of the SPARTA framework
CyberInflight team is part of the contributor list of the SPARTA framework. The last version published on July 18, 2023, adds more than 60...
Thales confirms its key role to provide cybersecurity for Galileo second generation to meet...
Thales has been notified by the European Space Agency (ESA), on behalf of the European Union Agency for the Space Programme (EUSPA) and the...
Coverage by CyberInflight of the Russian satellite telecom Dozor-Teleport Attack
CyberInflight (www.cyberinflight.com) is an independant consulting and business intelligence company dedicated to the topic of Aerospace Cybersecurity. CyberInflight’s goal is to raise the global cybersecurity...
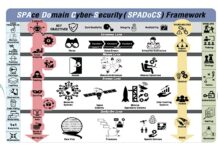
A comprehensive 3-day Space Domain Cybersecurity course organized around the SPAce Domain Cybersecurity (SpaDoCs)...
This article describes a comprehensive 3-day Space Domain Cybersecurity course organized around the SPAce Domain Cybersecurity (SpaDoCs) Framework.
Course Description
This Space Domain Cybersecurity course examines...