Below, I show some very funny memes on space security I created. Do not hesitate to download them and to share them.
SpaceSec, the Workshop on the Security of Space and Satellite Systems
SpaceSec is the Workshop on the Security of Space and Satellite Systems
https://spacesec.info/
SpaceSec 2023 took place on the 27 February 2023 in San Diego, California.
https://www.ndss-symposium.org/ndss-program/spacesec-2023/
The videos of the 2023 edition of the SpaceSec workshop have recently been uploaded, and you can view them for free and get an overview of current space security research topics! Also, in case you missed the excellent keynote by James Pavur this is your chance to view it again, where he gave us an extensive overview of open research topics.
All SpaceSec 2023 videos are avalaible here.
SpaceSec will be co-located with the Network and Distributed System Security Symposium (NDSS) in San Diego on March 1, 2024.
You can space submit your security research project.
They will have two deadlines:
– December 7, 2023
– January 12, 2024.
They accept 4-page and 8-page papers on all aspects of space security. This is the perfect opportunity to publish your insights, vetted by a rigorous peer review of academic experts on the subject.
They are accepting papers from an extensive spectrum of space security topics, including space system security, networks and communication security, privacy and usability of space systems, and space security strategies.
My work about the Viasat attack analysis featured at the BSIDES St. Louis 2023 hacking education conference
I’m very proud to be featured by Tim Fowler in his presentation at BSIDES St. Louis 2023 hacking education conference. Tim Fowler is an offensive security analyst at Black Hills Information Security.
Tim mentionned my work about the Viasat attack analysis:
- I compared the 4 frameworks that can be used for the space sector: MITRE ATT&CK, SPARTA, SPACE-SHIELD and TREKS.
- I explain why I choose the MITRE ATT&CK Framework
- I identified Tactics, Techniques and Procedures (TTPs) from the MITRE ATT&CK matrix that have been used by the hackers
- I mapped them on the MITRE ATT&CK Navigator in order to have the complete attack chain.
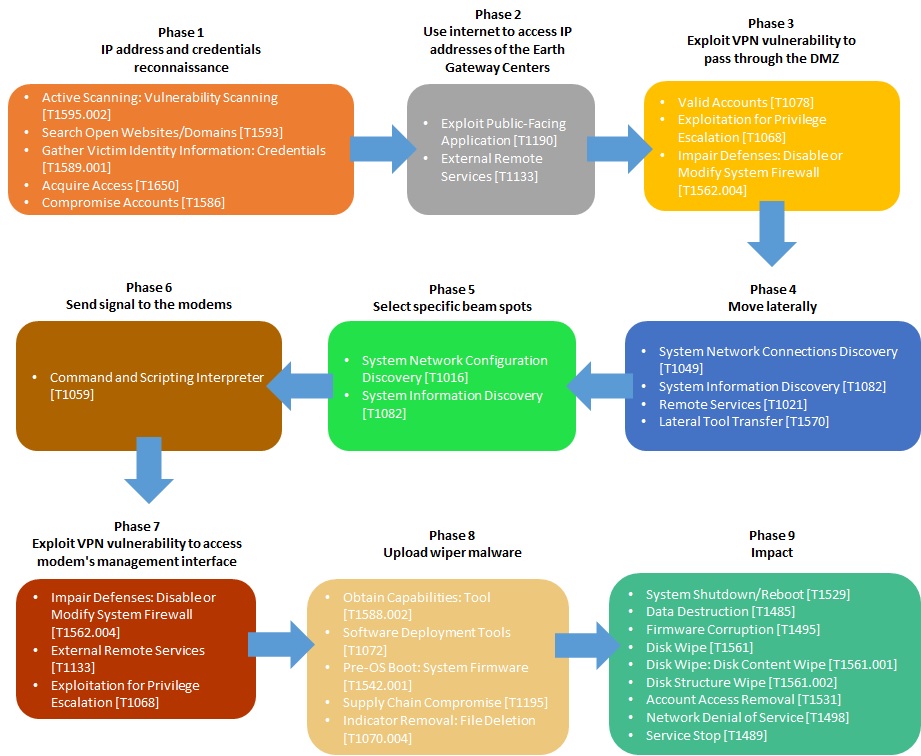
- I drawn a diagram as a Cyber Kill Chain showing all TTPs mapped on the entire attack life cycle of the Viasat cyber attack.
Thank’s again to Tim Fowler to have referenced my work in his talk at BSIDES St. Louis.
BSIDES St. Louis 2023 is a hacking education conference that took place on Oct 14, 2023 at St. Charles Community College in Missouri state (United States).
The presentation of Tim Fowler is called: A brief introduction to cybersecurity in Space; The Past, Present, & Future.
To know more
- Slides for this webcast available here (PDF)
- My article about the analysis of the Viasat cyber attack with the MITRE ATT&CK framework
- My LinkedIn group about Space Cybersecurity Community
DroneSec, a private intelligence agency for drone threats, that provides UAS Threat Intelligence and drone security training
DroneSec is a private intelligence agency for drone threats. DroneSec provides drone threat intelligence solutions to protect people and drones from malicious drones and people.
DroneSec provides the Notify UAS Threat Intelligence Platform for real-time visibility of drone threats. DroneSec solutions allow to put organizations 10 steps ahead of the threat.
DroneSec are pioneers in UAS Threat Intelligence. Their leading intelligence subscription service provides organizations with the latest emerging trends, threat actor TTPs, technology types and component analysis.
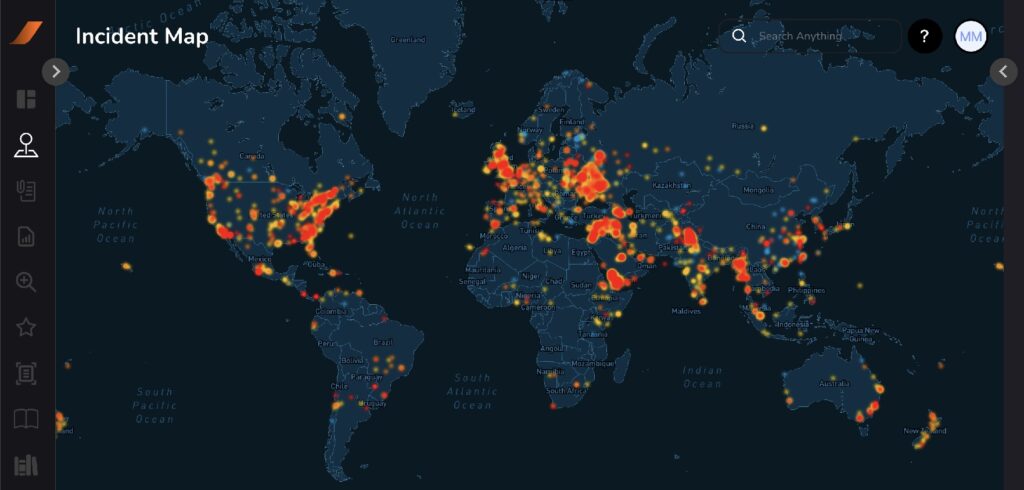
DroneSec provides also drone security and C-UAS training. Their courses have helped train organisations in offensive and defensive drone operations.
DroneSec Courses and training
Find below the Featured Courses. This includes three courses : Drone Security Fundamentals, Regulations and SECOPS. These three courses can be taken individually, or together as a bundle (recommended) to achieve certification.
The DROSINT and C-UAS Site Vulnerability courses can be taken only individually.
Our readers can get the following discount code for 10% off the course fees : SPACESECURITY
Participants will come away with a comprehensive understanding of:
- Drones, Counter-Drone and UTM Systems
- Current and future threat vectors and risk surface
- Various case studies, methodologies and threat modelling techniques
Participants will come away with a comprehensive understanding of:
- Drones, Counter-Drone and UTM system legal requirements
- Problems, Case Studies and Precedents within the Industry
- Current and future regulatory requirements and considerations
Drone SecOps: Offense & Defense
Participants will come away with a comprehensive understanding of:
- Security Risks and Attack Vectors within the Drone Industry
- Cyber, Physical and Kinetic Security Vectors
- Responding to, Simulating and Preparing for Intrusions
Beginner to Advanced: Drone Security Bundle
This bundle courses cover the entire drone ecosystem. Fundamental drone security concepts, counter-drone essentials and actionable playbooks based on threat-intelligence, and DroneSec case studies are included.
DroneSec Conferences
The State of Drone Security: Analysing 1000+ drone incidents – Mike Monnik (DroneSec) GDSN #2
Global Drone Security Network #2
AAUS RPAS in Australian Skies 2022 – Unique Trends in the Malicious use of RPAS
To know more
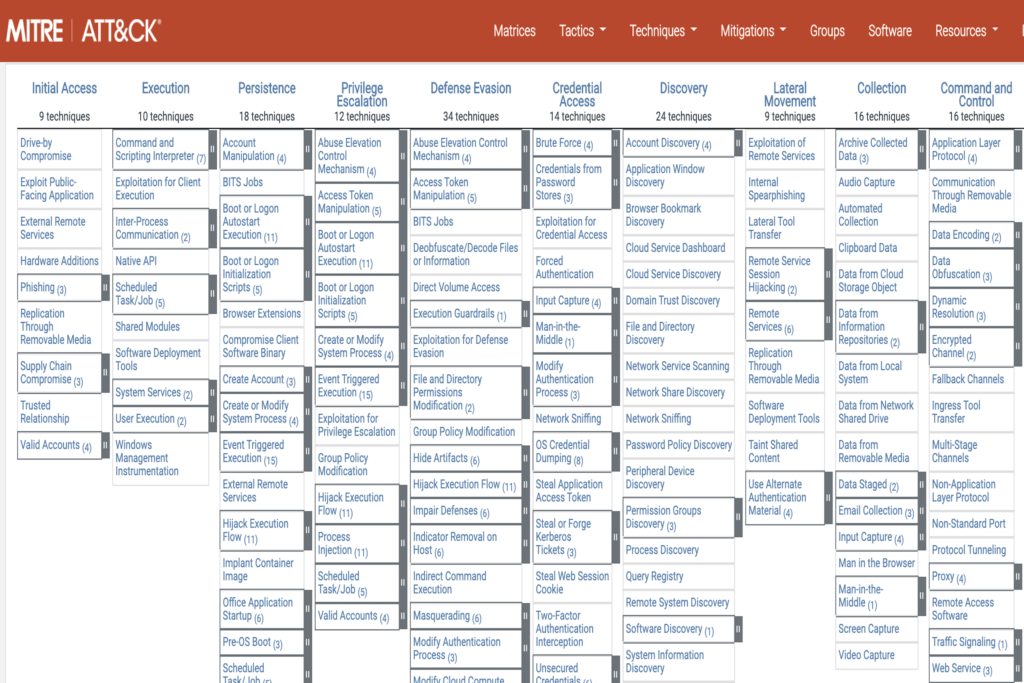
MITRE realeased ATT&CK v14 with improvements to Detections, ICS, Mobile
🔥 On 31 October 2023, the MITRE Corporation realeased ATT&CK v14, the new version of its framework.
This new version includes significant improvements to Detections, ICS, Mobile.
In this article, we summarize the biggest changes : and will go through more details.
🔥 Find below the Key Highlights of ATT&CK v14
👉 ATT&CK Version 14 contains 760 Pieces of Software, 143 Groups, and 24 Campaigns. Broken out by domain:
- ✔️ Enterprise: 201 Techniques, 424 Sub-Techniques, 141 Groups, 648 Pieces of Software, 23 Campaigns, 43 Mitigations, and 109 Data Sources
- ✔️ Mobile: 72 Techniques, 42 Sub-Techniques, 8 Groups, 108 Pieces of Software, 1 Campaign, 12 Mitigations, and 15 Data Sources
- ✔️ ICS: 81 Techniques, 13 Groups, 21 Pieces of Software, 52 Mitigations, 3 Campaigns, 14 Assets, and 34 Data Sources
👉 ATT&CK v14 features 14 inaugural Assets (Assets represent the devices and systems commonly found within Industrial Control System environments), representing the primary functional components of the systems associated with the ICS domain. These Asset pages include in-depth definitions, meticulous mappings to techniques, and a list of related Assets.
🔥 MITRE has published a blog post detailing some of the major updates in ATT&CK v14, as well as release notes listing new techniques and version changes. A detailed changelog is also available.
More about MITRE ATT&CK framework
The MITRE ATT&CK framework is a globally recognized knowledge base and methodology for understanding, organizing, and classifying cyber threats and tactics used by adversaries during different stages of a cyber attack. ATT&CK stands for Adversarial Tactics, Techniques, and Common Knowledge.
The framework was developed by MITRE, a not-for-profit organization that operates federally funded research and development centers (FFRDCs) to address various challenges faced by the U.S. government. However, the framework has gained widespread adoption in the cybersecurity community and is used by organizations around the world.
The MITRE ATT&CK framework provides a comprehensive model that describes the entire lifecycle of a cyber attack, from initial reconnaissance and weaponization to lateral movement, data exfiltration, and impact. It consists of a matrix that outlines various tactics and techniques employed by adversaries, along with information on the platforms they target (e.g., Windows, macOS, Linux) and the types of software they use.
The framework is organized into several categories, including Initial Access, Execution, Persistence, Privilege Escalation, Defense Evasion, Credential Access, Discovery, Lateral Movement, Collection, Exfiltration, and Impact. Each category is further divided into specific techniques and sub-techniques that adversaries may employ.
For each technique, the framework provides detailed information on how it works, the potential impact, and real-world examples of its usage by known threat actors. This knowledge base allows organizations to better understand the tactics and techniques employed by adversaries and assists in building effective defensive strategies and improving incident response capabilities.
By utilizing the MITRE ATT&CK framework, organizations can map observed adversary behaviors to specific techniques, identify security gaps, prioritize defenses, develop threat intelligence, and share information with the broader cybersecurity community. The framework serves as a common language and reference point for cybersecurity professionals, enabling them to collaborate and exchange knowledge on emerging threats and effective defense strategies.
Overall, the MITRE ATT&CK framework plays a crucial role in enhancing cybersecurity awareness and readiness, facilitating the development of proactive defense measures, and improving the overall resilience of organizations against cyber attacks.
Go to the MITRE ATT&CK framework here.
Very proud to have earned the Space Domain Cybersecurity digital badge from Teaching Science and Technology, Inc.
🚀 I’m proud to took part of the 3-day Space Domain Cybersecurity course provided by Teaching Science & Technology, Inc. (TSTI) in partnership with Space ISAC. and to have earned the Space Domain Cybersecurity digital badge.
🗓️ I took part in this course on my own time and as an evening course. The course is organized around the SPAce Domain Cybersecurity (SpaDoCs) Framework.
📑 The SpaDoCs Framework provides a comprehensive and systematic model for understanding and tackling all critical issues of cybersecurity in the space domain.
🛰️ As cybersecurity professional and space domain passionate, my wish was to develop my knowledge and skills and to better understand cybersecurity for space systems.
💪 In this course, I gained knowledge and skills to secure the space mission lifecycle. The space domain is examined layer by layer starting from the enterprise layer, then drilling down through mission, system and DevSecOps layers. Threats and vulnerabilities at each layer are highlighted. Finally, first principles of cybersecurity are discussed (domain separation, process isolation, etc.) as well as key enablers (vision, strategy, etc.) to help frame plans for action to address the cybersecurity issues exposed by this course.
After the 18-hour course, I now have an understanding of the Space Domain Cybersecurity Framework. I can define key threats and vulnerabilities that may affect space missions and systems and explain the impact on each layer of the space domain. I can apply cybersecurity first principles throughout the mission lifecycle and use these concepts to identify issues and potential mitigations. I can discuss NIST and other guidance, including the upcoming CMMC requirements.
👊 It was a great opportunity for me to explore #cybersecurity challenges specific to space missions. Now, I own skills to secure cyber environments throughout the space mission lifecycle.
🙏 I would like to thanks :
- Dr. Bruce Chesley, Ph.D. an experienced space program manager and industry executive
- Terri Johnson, an #cybersecurity management instructor at the University of Colorado Colorado Springs (UCCS)
👉 All informations about this course here
🏅 Check my certification digital badge here
👉 More about the SPAce Domain Cybersecurity (#SpaDoCs) Framework here
Live Webinar on Aerospace Cybersecurity: Satellite Hacking
Find below the first ever webinar by PenTest Mag! Hosted by Timothy Hoffman, the talk will evolve around the topic of the online course – “Aerospace Cybersecurity: Satellite Hacking”, designed and instructed by Angelina Tsuboi.
During the event, the discussion will touch the practical aspects of the fascinating field of aerospace cybersecurity. You will have a chance to listen about tools, techniques, and even real-life case studies from the realm of satellite ethical hacking. After the talk, there will be a chance to ask our instructor some questions. Also, those of participants, who have not decided to enroll yet, will get a chance to seize a special deal to secure their seats.
To know more about the course : « Aerospace Cybersecurity: Satellite Hacking » made by Angelina Tsuboi in collaboration with PenTestMag, go to the following link.
An analysis of the Viasat cyber attack with the MITRE ATT&CK® framework
Disclaimer
To do this analysis of the Viasat cyber attack, I used the open-source intelligence (1) of the team composed by Nicolò Boschetti (Cornell University), Nathaniel Gordon (Johns Hopkins University) and Gregory Falco (Cornell University). In their open-source intelligence, they reconstructed the lifecycle of the attack. They specified that however, without first-hand knowledge of ViaSat’s systems, they cannot be certain about their hypothesis. With their open-source intelligence, they schematized the entire attack lifecycle in a diagram.
Viasat’s statement (2) on Wednesday, March 30th, 2022 provides a somewhat plausible but incomplete description of the attack.
In a statement disseminated to journalists (3), Viasat confirmed the use of the AcidRain wiper in the February 24th attack against their modems.
At the DefCon 31, Mark Colaluca and Nick Saunders from Viasat presented a talk named “Defending KA-SAT“. During this talk, they argued not to believe everything that you can read on the internet. It’s often simply inaccurate. They told that there is no evidence or proof of the claims. There is no evidence of any compromise or tampering with Viasat modem software or firmware images and no evidence of any supply-chain interference. Regarding, the possibility that wipermalware was deployed and erased the hard drives of the modems, they answered that modems don’t have hard drives.
At the Black Hat USA 2023, Mark Colaluca , Craig Miller , Nick Saunders , Michael Sutton , Kristina Walter from Viasat presented a talk named “Lessons Learned from the KA-SAT Cyberattack: Response, Mitigation and Information Sharing“. This presentation will provide the most detailed public presentation of the KA-SAT event. Viasat will share the story of how it responded and performed a rapid forensic on several impacted terminals. This presentation will explain details around the forensic analysis that have not previously been publicly shared by Viasat, as well as the process of reverse engineering the malicious toolkit to verify it would produce the observed flash memory effects. Both Viasat and NSA will offer their lessons learned from the cyberattack and advise on how commercial and government organizations can follow this model to partner both in response to and preparation for future attacks.
Introduction
In this article, we will go through the Viasat cyber attack that occured on 24 February, 2022. The goal is to do a modelisation of this attack based on the MITRE ATT&CK framework.
The first question will be to explain why to use the MITRE ATT&CK framework to do this analysis while there are others frameworks and methodologies that can be used for the space sector.
The next work will be to identify Tactics, Techniques and Procedures (TTPs) from the MITRE ATT&CK matrix that have been used by the hackers during the Viasat attack. To learn more about the MITRE ATT&CK framework, you can go to this article about the ATT&Ck v13 release.
Once TTP identified, we will map the TTPs on the ATT&CK Navigator in order to have the complete attack chain as a cyber kill chain.
About the Viasat hack in brief
The Viasat hack was a cyberattack on American communications company Viasat affecting their KA-SAT network, on 24 February, 2022.
Thousands of Viasat modems got hacked by a “deliberate … cyber event”. Thousands of customers in Europe have been without internet for a month since. During the same time, remote control of 5,800 wind turbines belonging to Enercon in Central Europe was affected.
According to Viasat, the attacker used a poorly configured virtual private network appliance to gain access to the trusted management part of the KA-SAT network. The attackers then issued commands to overwrite part of the flash memory in modems, making them unable to access the network, but not permanently damaged. The satellite itself and its ground infrastructure were not directly affected.
About Viasat
Viasat is an American communications company based in Carlsbad, California, with additional operations across the United States and worldwide. Viasat is a provider of high-speed satellite broadband services and secure networking systems covering military and commercial markets
Which framework using ?
The first question is which framework to use to do this analysis ? At this time, there are 5 frameworks and methodologies that can be used for the space sector :
- MITRE ATT&CK is a globally-accessible knowledge base of adversary tactics and techniques based on real-world observations. You can learn more about MITRE AT&CK in our article here.
- SPARTA is the Aerospace Corporation’s Space Attack Research and Tactic Analysis. SPARTA is an ATT&CK® like knowledge-base framework but for Space Missions. SPARTA matrix is intended to provide unclassified information to space professionals about how spacecraft may be compromised due to adversarial actions across the attack lifecycle. You can learn more about SPARTA in our article here.
- SPACE-SHIELD is the Space Attacks and Countermeasures Engineering Shield from ESA. SPACE-SHIELD is an ATT&CK® like knowledge-base framework for Space Systems. It is a collection of adversary tactics and techniques, and a security tool applicable in the Space environment to strengthen the security level. The matrix covers the Space Segment and communication links, and it does not address specific types of mission. You can learn more about SPACE-SHIELD in our article here.
- TREKS is the Targeting, Reconnaissance, & Exploitation Kill-Chain for Space Vehicles Cybersecurity Framework. TREKS is a new Cybersecurity Framework that highlights the unique kill chain for the space vehicle. It’s a Cybersecurity Framework released by Dr. Jacob Oakley after more than five years spent researching and working on space system cybersecurity. You can learn more about TREKS in our article here.
- SpaDoCs, or the Space Domain Cybersecurity Framework, is a comprehensive and systematic model designed to address cybersecurity challenges in the space domain. Developed to bridge the gap between space and cyber domains, SpaDoCs aims to enhance collaboration and information sharing across mission, company, international, and government boundaries. You can learn more about SpaDoCs in our article here.
I did a quick comparaison in this article, of all the released Cybersecurity Frameworks for Space Sector
SPARTA is a framework but for spacecraft and space missions. SPARTA doesn’t cover ground segment. The entire Viasat attack took place on Earth, on a ground-based network and on a conventional information system. So, there is no reason to use SPARTA, SPACE-SHIELD or TREKS. MITRE ATT&CK is a great framework, well suited for this analysis. To be more precise, we used the MITRE ATT&CK – Enterprise Matrix.
Quick overview and comparaison between MITRE ATT&CK and the Cyber Kill Chain
What is the Cyber Kill Chain?
“The cyber security kill chain model explains the typical procedure that hackers take when performing a successful cyber attack. It is a framework developed by Lockheed Martin derived from military attack models and transposed over to the digital world to help teams understand, detect, and prevent persistent cyber threats. While not all cyber attacks will utilize all seven steps of the cyber security kill chain model, the vast majority of attacks use most of them, often spanning Step 2 to Step 6.” (source : netskope.com)
What is in the MITRE ATT&CK Matrix?
“The MITRE ATT&CK matrix contains a set of techniques used by adversaries to accomplish a specific objective. Those objectives are categorized as tactics in the ATT&CK Matrix. The objectives are presented linearly from the point of reconnaissance to the final goal of exfiltration or impact.” (source : trellix.com)
Comparaison between the Cyber Kill Chain and the MITRE ATT&CK matrix
The table below compares the stages of the Cyber Kill Chain with those of the MITRE ATT&CK matrix
| Cyber Kill Chain | MITRE ATT&CK |
| Reconnaissance | Reconnaissance |
| Weaponization | Resource Development |
| Delivery | Initial Access |
| Exploitation | Execution |
| Installation | Persistence |
| Command and Control (C2) | Privilege Escalation |
| Actions on objectives | Defense Evasion |
| Credential Access | |
| Discovery | |
| Lateral Movement | |
| Collection | |
| Command and Control (C2) | |
| Exfiltration | |
| Impact |
Mapping the Viasat hack with TTPs
To do this work, we mainly used 3 articles, documents or papers detailed below :
- [1] Space Cybersecurity Lessons Learned from The ViaSat Cyberattack from Nicolò Boschetti (Cornell University), Nathaniel Gordon (Johns Hopkins University) and Gregory Falco (Cornell University)
- [2] KA-SAT Network cyber attack overview by Viasat
- [3] AcidRain | A Modem Wiper Rains Down on Europe by SentineOne Team
Best Practices for MITRE ATT&CK Mapping
MITRE ATT&CK is often used to identify and analyze adversary behavior. CISA (Cybersecurity and Infrastructure Security Agency) released a guidance to help analysts accurately and consistently map adversary behaviors to the relevant ATT&CK techniques as part of cyber threat intelligence (CTI)—whether the analyst wishes to incorporate ATT&CK into a cybersecurity publication or an analysis of raw data.
We used these best Practices for MITRE ATT&CK® Mapping that you can find here :Best Practices for Mapping to MITRE ATT&CK (cisa.gov)
Mapping the Viasat hack with TTPs
Through open-source intelligence, the team [1] composed by Nicolò Boschetti (Cornell University), Nathaniel Gordon (Johns Hopkins University) and Gregory Falco (Cornell University) reconstructed the lifecycle of the attack.
They specified that “however, without first-hand knowledge of ViaSat’s systems, we cannot be certain about our hypothesis“.
They schematized the entire attack life cycle in the diagram below (from document [1])
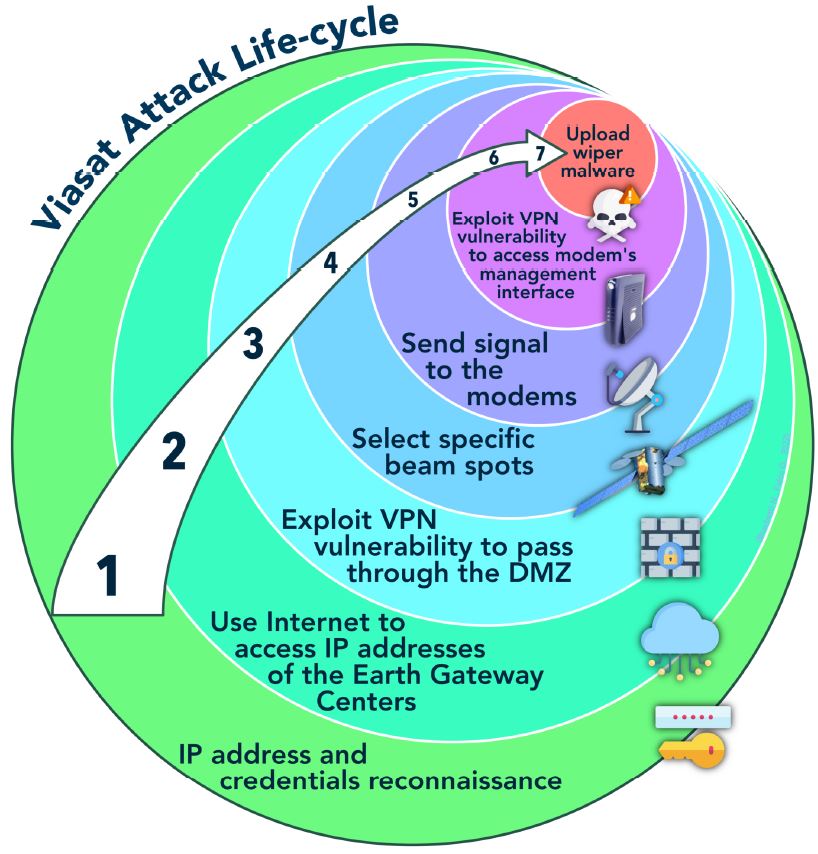
We will use this diagram to identify TTPs used by attackers at each steps of the attack
Phase 1 : IP address and credentials reconnaissance
[1] “In 2021, Fortinet disclosed an attack on their VPN “Fortigate” that exploited a vulnerability discovered in 2019 (editor’s note: CVE-2018-13379). The allegedly Russian hacker group Groove stole and published credentials of almost 500,000 IP addresses in the same year.”
At this phase, we identified the following TTPs :
| Tactic | Technique |
| Reconnaissance | [T1595.002] Active Scanning: Vulnerability Scanning |
| [T1593] Search Open Websites/Domains | |
| [T1589.001] Gather Victim Identity Information: Credentials | |
| Resource Development | [T1650] Acquire Access |
| [T1586] Compromise Accounts |
Phase 2 : Use internet to access IP addresses of the Earth Gateway Centers
[1] “ViaSat has shared that the initial attacker intrusion point was via the internet. Skylogic’s control servers, the Gateway Earth Stations, and the Surfbeam2 modems rely on VPN appliances produced by the company Fortinet as indicated by the security researcher Ruben Santamarta.”
At this phase, we identified the following TTPs :
| Tactic | Technique |
| Initial Access | [T1190] Exploit Public-Facing Application |
| [T1133] External Remote Services |
Phase 3 : Exploit VPN vulnerability to pass through the DMZ
[2] “Subsequent investigation and forensic analysis identified a ground-based network intrusion by an attacker exploiting a misconfiguration in a VPN appliance to gain remote access to the trusted management segment of the KA-SAT network.”
[1] “It is known that Fortinet released a patch to address the vulnerability, but it is unclear if ViaSat’s operator, Skylogic, ever deployed the patch. Therefore, we can surmise that the attacker used the unpatched VPN to access Skylogic’s Gateway Earth Stations or POP server from the open internet.”
At this phase, we identified the following TTPs :
| Tactic | Technique |
| Initial Access | [T1078] Valid Accounts |
| Privilege Escalation | [T1068] Exploitation for Privilege Escalation |
| Defense Evasion | [T1562.004] Impair Defenses: Disable or Modify System Firewall |
Phase 4 : Move laterally
[2] “The attacker moved laterally through this trusted management network to a specific network segment used to manage and operate the network” of modems.
[1] “This access, or privilege escalation, allowed the attacker to pass the DMZ and access the bent-pipe satellite intranet (the trusted management network) tunneling their way to the Surfbeam2 modem. This process is confirmed by ViaSat’s statement”
At this phase, we identified the following TTPs :
| Tactic | Technique |
| Discovery | [T1049] System Network Connections Discovery |
| [T1082] System Information Discovery | |
| Lateral Movement | [T1021] Remote Services |
| [T1570] Lateral Tool Transfer |
Phase 5 : Select specific beam spots
[1] “Not all ViaSat modems were targeted. This can be explained by an operator’s capability at the Gateway Earth Stations to select which of KA-SAT’s 82 geographic cells receive signal. This implies that the attacker specified which geographic cells (and their respective modems) would receive the signal with the malicious commands.”
At this phase, we identified the following TTPs :
| Tactic | Technique |
| Discovery | [T1016] System Network Configuration Discovery |
| [T1082] System Information Discovery |
Phase 6 : Send signal to the modems
[2] “and then used this network access to execute legitimate, targeted management commands on a large number of residential modems simultaneously.”
[1] “The attacker specified which geographic cells (and their respective modems) would receive the signal with the malicious commands.”
At this phase, we identified the following TTPs :
| Tactic | Technique |
| Execution | [T1059] Command and Scripting Interpreter |
Phase 7 : Exploit VPN vulnerability to access modem’s management interface
[1] “Once at the modem, the attacker again escalated privilege using the unpatched VPN, enabling their manipulation of the modem’s management.”
At this phase, we identified the following TTPs :
| Tactic | Technique |
| Defense Evasion | [T1562.004] Impair Defenses: Disable or Modify System Firewall |
| Initial Access | [T1133] External Remote Services |
| Privilege Escalation | [T1068] Exploitation for Privilege Escalation |
Phase 8 : Upload wiper malware
[2] “Specifically, these destructive commands overwrote key data in flash memory on the modems, rendering the modems unable to access the network, but not permanently unusable.”
[1] “The modem likely had limited or no firmware authentication requirements, therefore the attacker was able to provide a ‘valid’ firmware update, installing an ELF binary dubbed “AcidRain” which deleted data from the modem’s flash memory.”
[3] “The threat actor used the KA-SAT management mechanism in a supply-chain attack to push a wiper designed for modems and routers,”
[3] “In a statement disseminated to journalists, Viasat confirmed the use of the AcidRain wiper in the February 24th attack against their modems.”
At this phase, we identified the following TTPs :
| Tactic | Technique |
| Resource Development | [T1588.002] Obtain Capabilities: Tool |
| Execution | [T1072] Software Deployment Tools |
| Initial Access | [T1195] Supply Chain Compromise |
| Defense Evasion | [T1070.004] Indicator Removal: File Deletion |
| Persistence | [T1542.001] Pre-OS Boot: System Firmware |
Phase 9 : Impact
[2] “Ultimately, tens of thousands of modems that were previously online and active dropped off the network, and these modems were not observed attempting to re-enter the network. The attack impacted a majority of the previously active modems within Ukraine, and a substantial number of additional modems in other parts of Europe.”
[2] “Specifically, these destructive commands overwrote key data in flash memory on the modems, rendering the modems unable to access the network, but not permanently unusable.”
[1] “We hypothesize that the attack’s spillover effects in Germany and other European states are due to either an error when selecting the geographic cells that received the malicious signal, or simply the selection of cells that contained Ukrainian territory with overlap of other EU countries”
At this phase, we identified the following TTPs :
| Tactic | Technique |
| Impact | [T1529] System Shutdown/Reboot |
| [T1485] Data Destruction | |
| [T1495] Firmware Corruption | |
| [T1561] Disk Wipe | |
| [T1561.001] Disk Wipe: Disk Content Wipe | |
| [T1561.002] Disk Structure Wipe | |
| [T1531] Account Access Removal | |
| [T1498] Network Denial of Service | |
| [T1489] Service Stop |
Summary of MITRE ATT&CK TTPs observed in the Viasat cyber attack
The following table presents all TTPs that have been used by the hackers during the Viasat attack.
| Tactic | Technique | Description |
| Reconnaissance | [T1595.002] | Active Scanning: Vulnerability Scanning |
| [T1593] | Search Open Websites/Domains | |
| [T1589.001] | Gather Victim Identity Information: Credentials | |
| Resource Development | [T1650] | Acquire Access |
| [T1586] | Compromise Accounts | |
| [T1588.002] | Obtain Capabilities: Tool | |
| Initial Access | [T1190] | Exploit Public-Facing Application |
| [T1133] | External Remote Services | |
| [T1078] | Valid Accounts | |
| [T1195] | Supply Chain Compromise | |
| Execution | [T1059] | Command and Scripting Interpreter |
| [T1072] | Software Deployment Tools | |
| Persistence | [T1542.001] | Pre-OS Boot: System Firmware |
| Privilege Escalation | [T1068] | Exploitation for Privilege Escalation |
| Defense Evasion | [T1562.004] | Impair Defenses: Disable or Modify System Firewall |
| [T1070.004] | Indicator Removal: File Deletion | |
| Discovery | [T1049] | System Network Connections Discovery |
| [T1082] | System Information Discovery | |
| Lateral Movement | [T1021] | Remote Services |
| [T1570] | Lateral Tool Transfer | |
| Impact | [T1529] | System Shutdown/Reboot |
| [T1485] | Data Destruction | |
| [T1495] | Firmware Corruption | |
| [T1561] | Disk Wipe | |
| [T1561.001] | Disk Wipe: Disk Content Wipe | |
| [T1561.002] | Disk Structure Wipe | |
| [T1531] | Account Access Removal | |
| [T1498] | Network Denial of Service | |
| [T1489] | Service Stop |
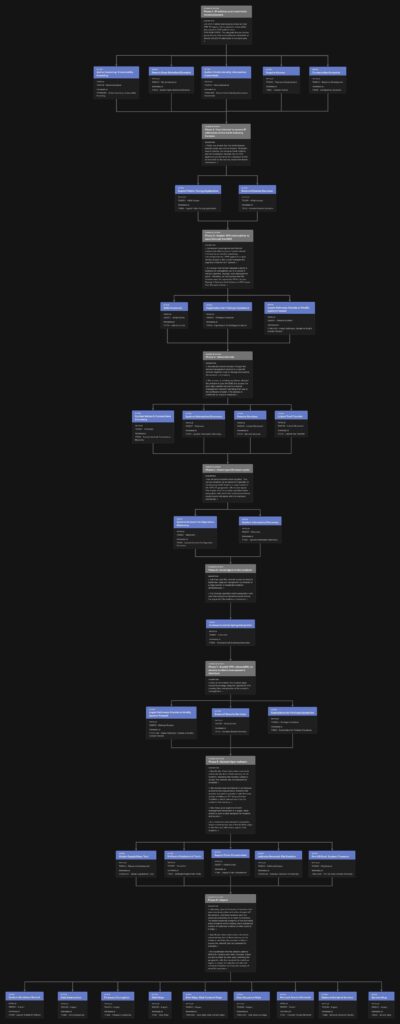
The following table presents all TTPs mapped on the ATT&CK Navigator in order to have the complete attack chain as a cyber kill chain.
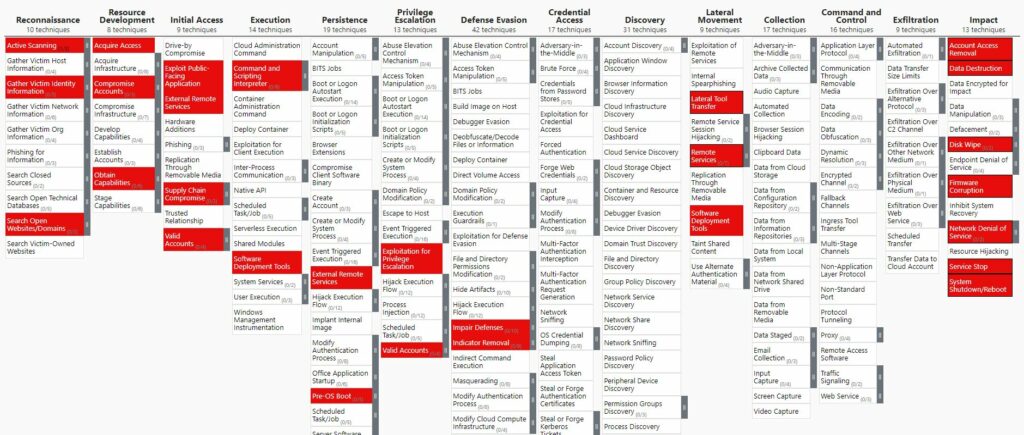
You can download the Excel version here.
You can also download the JSON file here and open it with the ATT&CK Navigator with the option “Open Existing Layer” and “Upload from local”
The following diagram presents all TTPs mapped on the entire attack life cycle of the Viasat cyber attack. This diagram is inspired from the schema of the entire attack life cycle done by the team [1] composed by Nicolò Boschetti (Cornell University), Nathaniel Gordon (Johns Hopkins University) and Gregory Falco (Cornell University).
Viasat Cyber Attack modeled with the MITRE Attack Flow Builder
Using all results of this work, I utilized the Attack Flow Builder to deconstruct the Viasat cyber attack, meticulously tracing each stage of the intrusion.
By systematically documenting the initial access vector, tracking lateral movement within the network, and visualizing the execution of the malicious firmware update, I created a detailed forensic map of the attack’s progression.
The full article about this work can be found here.
List of remaining work
Following this study, there is still a great deal of work to be done. See below for a list of topics still to be dealt with. If any of you are interested, please contact me here.
- Describing sequences of adversary behaviors in the Attack flow data model
- Trying to highlight the vulnerabilities exploited by the attackers
- Trying to propose countermeasures that could be used to mitigate the attack. Mitigation chapter for each techniques in the MITRE ATT&CK framework can be used
- Trying to map countermeasures on the MITRE D3FEND™ Matrix
Main References
- [1] Space Cybersecurity Lessons Learned from The ViaSat Cyberattack from Nicolò Boschetti (Cornell University), Nathaniel Gordon (Johns Hopkins University) and Gregory Falco (Cornell University)
- [2] KA-SAT Network cyber attack overview by Viasat
- [3] AcidRain | A Modem Wiper Rains Down on Europe by SentineOne Team
Others References
- Threat Intelligence Alert: Russia/Ukraine Conflict by NCCGroup
- Threat Update: AcidRain Wiper by Splunk
- New Sandworm Malware Cyclops Blink Replaces VPNFilter by CISA
- Mystery solved in destructive attack that knocked out >10k Viasat modems by Arstechnica
- VIASAT incident: from speculation to technical details by Reversemode
- AcidRain Wiper Suspected in Satellite Broadband Outage in Europe by Fortiguard
- NSA | Protecting VSAT Communications via NSA
- Strengthening Cybersecurity of SATCOM Network Providers and Customers by CISA
- Ukraine: Disk-wiping Attacks Precede Russian Invasion by Symantec
- Russia/Ukraine Update – November 2022 by Optiv
- Cyber Threat Handbook 2022 by Thales
- An Overview of the Increasing Wiper Malware Threat by Fortinet
- Characterizing Cyber Attacks against Space Systems with Missing Data: Framework and Case Study by Ekzhin Ear, Jose L. C. Remy, Antonia Feffer, and Shouhuai Xu – Department of Computer Science – University of Colorado Colorado Springs
- Wiper Malware: Purposes, MITRE Techniques, and Attacker’s Trade-Offs by Julian-Ferdinand Vögele (Threat Research @ Recorded Future)
- Best Practices for MITRE ATT&CK® Mapping by CISA
- Video Youtube : DEF CON 31 – Defending KA-SAT by Mark Colaluca and Nick Saunders
- Youtube Video : Black Hat USA 2023 – Lessons Learned from the KA-SAT Cyberattack: Response, Mitigation and Information Sharing by Mark Colaluca , Craig Miller , Nick Saunders , Michael Sutton , Kristina Walter
New upcoming course : “Aerospace Cybersecurity: Satellite Hacking” made by Angelina Tsuboi in collaboration with PenTestMag
We are very excited to announce a new upcoming course, “Aerospace Cybersecurity: Satellite Hacking” led by Angelina Tsuboi in collaboration with PenTestMag.
This comprehensive course will delved into the captivating world of satellite hacking while emphasizing strategies to safeguard these critical systems. Key topics will cover included satellite communication basics, tracking and identification methods, vulnerabilities and threats, signal analysis, and protocol exploitation. This course not only provided insights into hacking techniques but also stressed the significance of protecting satellites from potential attacks.
This 18-hours course will dive deep into the groundbreaking world of aerospace cybersecurity by teaching the skills necessary to conduct reconnaissance, communication dissection, decoding, and vulnerability analysis of satellite systems through interactive activities and tutorials.
Throughout this course, you will explore the fundamentals of satellite hacking, starting with hands-on CTF exercises that teach the basics through practical application by utilizing online tools and scripts.
Topics covered in this course include
- Satellite Identification & Reconnaissance using OSINT tools
- Orbital Parameters and Mechanics
- Two-Line Element Set Extraction and Interpretation
- Satellite Communications & Frequency Analysis
- Satellite Onboard Systems & SATCOM
- Intercepting Satellite Signals
- Reverse Engineering Satellite Communications
- Predicting and Tracking Satellite Passes
- SDR tools for Communication Extraction
- Hijacking and Control Explanation
- Jamming & Spoofing & Eavesdropping Mitigation
- Attack Mitigation Strategies
In conclusion, this Satellite Cybersecurity course will provide a comprehensive understanding of satellite hacking techniques, along with the tools and strategies required to defend against them using digital forensics and attack vector detection. Sign up for the course at the link below!
https://pentestmag.com/product/aerospace-cybersecurity-satellite-hacking/
About course instructor Angelina Tsuboi
Angelina Tsuboi is a programmer, mechatronics developer, and cybersecurity researcher who is currently working for NASA. She is interested in educating others about the exciting field of aerospace cybersecurity in conjunction with developing her own programs and research in the field.
About PenTest Magazine
PenTest Magazine is a monthly downloadable IT security magazine and an online course platform, devoted to penetration testing and all things on offensive cybersecurity. It features articles by penetration testing specialists and enthusiasts, experts in vulnerability assessment and management. We cover all aspects of pen testing, from theory to practice, from methodologies and standards to tools and real-life solutions. Each magazine features a cover focus, and articles from our regular contributors, covering IT security news and up-to-date topics.
Course general information



$399.00 $349.00
Course format
- Self-paced
- Pre-recorded
- Accessible even after you finish the course
- No preset deadlines
- Materials are video, labs, and text
- All videos captioned
More information and registration
You can find out more about the course and sign up here.
Indiana University – Kelley School of Business launches a new academic program dedicated to cybersecurity of space systems
Russia’s cyberattack on ViaSat on the eve of its invasion of Ukraine put the cyber fragility of space systems high on the agenda and the need to secure them a top priority. Yet, space companies lack the required knowledge and the U.S. lacks skilled personnel and has no training programs. Until now.
Indeed, I will speak about the first program dedicated to cybersecurity of space systems.
This is a 10-week synchronous teaching and interactive webinar series that will provide participants with in-depth understanding of the cyber threats to space systems and the tools to develop and implement effective strategies for managing cyber risks to space-based infrastructure.
This new space-cybersecurity program focused on the unique issues arising in the context of protecting space-based assets from cyber attacks.
This program lasts 10 weeks and consists of a 60 minute live virtual session and one to two hours of asynchronous work each week. Each course will be independently taught by an industry professional and the program leads.
After successfully completing this program, participants will be prepared to manage the cyber threats space-based assets.
In this program, participants will earn a digital badge that can be shared on social media platforms, including LinkedIn and could also earn 3 credit waivers toward either the Kelley School of Business (Indiana University) Executive Education Cybersecurity Management certificate (a 12 credit hour graduate certificate), which can then be applied to the MS in Cybersecurity Risk Management— or choose to apply the 3 credit waivers directly to the MS program.
This 10-week virtual instructor-led program runs Sept 11 to Nov 13.
You can find out more about the Program and sign up here.
The sky is definitely not the limit!